THREAT ANALYSIS AND SHARING WEBINAR SERIES
For the third webinar in the Threat Analysis and Sharing series, Internews’ Digital Forensics Consultant introduced the basic features of Cuckoo Sandbox, a software which can be used by digital first responders and researchers for automated analysis of malware.
Key Takeaways:
Cuckoo Sandbox is a tool to understand the behavior of a suspicious file when executed on a potential victim’s machine. Cuckoo runs the malicious file in a contained virtual environment, hence the label “Sandbox”.
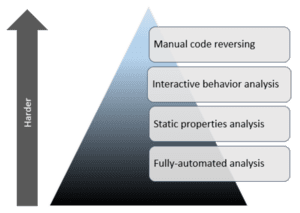
Cuckoo is valuable for initial automated triage in incident response. You can submit potentially malicious files and documents, file hashes, or URLs for “first look” analysis before putting a person on the job. Cuckoo can be configured to use any malware research ruleset (such as Virustotal, ReversingLabs, Koodous) and output data to threat information sharing platforms like MISP. You can also compare analysis across two different virtual machines.
Each analysis produces a report scoring the “maliciousness” of the data. The report will also detail the basic file information (size; type; hash), signatures describing all the action the malicious items takes when activated, and screenshots and any dropped files.
You can build a virtual environment to suit your research needs. Cuckoo can be configured to work with a variety of virtualization environments, which can run virtual machines with any operating system and software. All software must be installed, but some virtual machine builders can auto-install software packages for which you have licenses.
Your Sandbox is entirely customizable! Whether your virtual machine updates Windows, utilizes antivirus, or employs a firewall are all up to you. Generally speaking, the more vulnerable your system, the better for malware research. You can also decide whether or not to send files to VirusTotal for analysis.
We’re excited for the organizational security community to have access to a new tool to more effectively analyse digital threats against civil society!
