The following resource is a self-guided phishing analysis module for those who are new email analysis and threat information sharing.
Developed by Internews’ threat information sharing project MONITOR, this material is a result of synthesizing and extracting materials from previous technical training for new threat labs conducted under the project to facilitate community capacity building. For more information about the MONITOR project, please visit the program page.
Our goal is for information security practitioners to practice basic phishing analysis in a safe environment. The program team decided to start with phishing analysis due to the large amount of phishing campaigns targeting civil society and their cost-effective nature[1][2]. The resource was developed to help practitioners learn how to identify and extract key data from a phishing email, or indicators of compromise, that support further research and sharing.
This is a proof of concept with the potential to add on technical materials to refine and practice these skills in the future. Currently, the module and material is broken down as follows:
Introduction
- Learning Goals
- Pre-Requisites
- Tools Used (list)
- Environmental Setup (if applicable)
- Recommended Readings or Review
Online Lecture Materials
- Self-Guided Walkthrough
- Tools Review
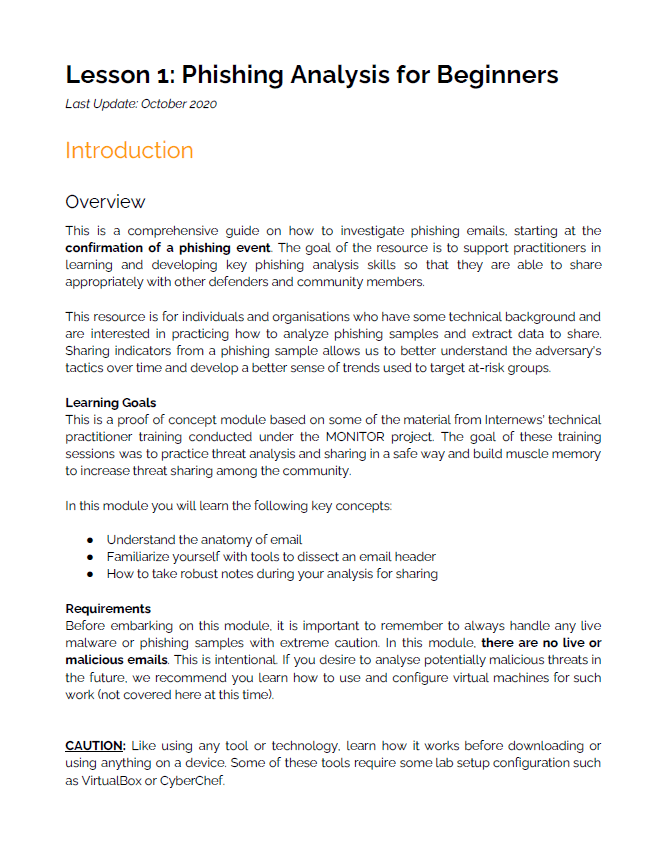
LESSON 1: PHISHING ANALYSIS FOR BEGINNERS
This is a comprehensive guide on how to investigate phishing emails, starting at the confirmation of a phishing event. The goal of the resource is to support practitioners in learning and developing key phishing analysis skills so that they are able to share appropriately with other defenders and community members. See below for the full lesson.
Lessons